Does anybody know if the P4 produces a .DAT file like the P3 or Inspire? If so, could someone please provide me with a P4 .DAT file. I could then determine if DatCon could be modified to analyze the P4 .DAT file. The instructions for retrieving a .DAT from the P3 might be helpful. https://datfile.net/retrieve.html
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
.DAT file for the P4?
- Thread starter BudWalker
- Start date
I messaged you back.Does anybody know if the P4 produces a .DAT file like the P3 or Inspire? If so, could someone please provide me with a P4 .DAT file. I could then determine if DatCon could be modified to analyze the P4 .DAT file. The instructions for retrieving a .DAT from the P3 might be helpful. https://datfile.net/retrieve.html
Sent from my iPhone using PhantomPilots mobile app
No enter flight data mode
MC Settings

Advanced under MC

Looked all over. Can't find it. Continuing to look.
Sent from my iPhone using PhantomPilots mobile app
MC Settings

Advanced under MC

Looked all over. Can't find it. Continuing to look.
Sent from my iPhone using PhantomPilots mobile app
@Fredz figured out how to retrieve the .DAT from the P4
http://www.phantompilots.com/threads/gui-version-of-datconverter.66872/page-5#post-719374
http://www.phantompilots.com/threads/gui-version-of-datconverter.66872/page-5#post-719374
- Joined
- Jun 25, 2015
- Messages
- 592
- Reaction score
- 128
ianwood
Taco Wrangler
I can also tell that transfering goes a lot quicker than before. 50 MB took a few seconds...
Thankfully!
@Fredz, can you or @BudWalker post up a quick how to in this thread for future reference?
Since you're on this thread I'm guessing you're looking for a .DAT from the P4 that you can convert using DatCon?Need some help. does anyone have sample FLYXXX.DAT (and ideally the associated video capture) that you can share with me. I'm having some issues w/ converting and just want to run a known good .DAT file through.
This doesn't start with FLY.... however this is a P4 DAT file you can download to see if you can get it to work.Need some help. does anyone have sample FLYXXX.DAT (and ideally the associated video capture) that you can share with me. I'm having some issues w/ converting and just want to run a known good .DAT file through.
ideally both P3 and P4 .DAT files. just looking for broader sample of files to make sure everything works and plan to run through DatCon at the end.Since you're on this thread I'm guessing you're looking for a .DAT from the P4 that you can convert using DatCon?
At this time we only can get the inner files of the copter via DJI-Assistant.
Here you can see two different files for one flight/switch on, a FC File and a Vision Modul File.
At the end of/or after? downloading they will be packed with an unknown procedure, I think.

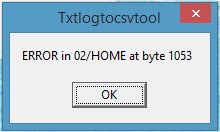
The .txt-file in TXTlogToCSVtool ends with a error at byte 1053.
H.
Here you can see two different files for one flight/switch on, a FC File and a Vision Modul File.
At the end of/or after? downloading they will be packed with an unknown procedure, I think.
The .txt-file in TXTlogToCSVtool ends with a error at byte 1053.
H.
I've had a couple of questions recently about the P4 .DAT file. I've relied on others to obtain some P4 .DAT files since I don't have access to a P4. Unlike the P3, the P4 requires that an app (DJI Assistant) be used to retrieve a .DAT file. Also, unlike the P3, the P4 produces 2 .DAT files for each flght; one for the flight controller, and one for the vision system.
The P3 .DAT is encoded, not encrypted. The encoding scheme allows a more energy efficient bus. If it were encrypted then it would be effectively impossible to extract information from the P3 .DAT. I looked at the P4 .DAT files and they are nothing like the P3 .DAT files. The methods I use to discover if the P4 .DAT is encoded didn't yield anything. I suspect the output of the DJI Assistant is either encrypted or compressed. If compressed then it's only a matter of time before someone determines the compression scheme. I haven't looked into this beyond trying a few of the obvious compression schemes.
A promising strategy would be to look at the USB link between the DJI Assistant and the P4. Packets on this link would likely not be encrypted or compressed. The data on this link might even be un-encoded; i.e. clear text. Pursuing this approach would require the use of a USB sniffer. If someone does this I can take a look at the data gathered and determine if the data can be used.
The P3 .DAT is encoded, not encrypted. The encoding scheme allows a more energy efficient bus. If it were encrypted then it would be effectively impossible to extract information from the P3 .DAT. I looked at the P4 .DAT files and they are nothing like the P3 .DAT files. The methods I use to discover if the P4 .DAT is encoded didn't yield anything. I suspect the output of the DJI Assistant is either encrypted or compressed. If compressed then it's only a matter of time before someone determines the compression scheme. I haven't looked into this beyond trying a few of the obvious compression schemes.
A promising strategy would be to look at the USB link between the DJI Assistant and the P4. Packets on this link would likely not be encrypted or compressed. The data on this link might even be un-encoded; i.e. clear text. Pursuing this approach would require the use of a USB sniffer. If someone does this I can take a look at the data gathered and determine if the data can be used.
- Joined
- Jun 25, 2015
- Messages
- 592
- Reaction score
- 128
I think the only way is to read the internal SD card of the P4. I opened it up, but the SD card is glued to the slot; I think using hot glue. I don't know what is below the card so I think it's almost impossible to remove it. See picture below. My P4 is currently open for a battery mod, so I could try...


Those small files could have some information that would help to determine how this thing works. Can you post a few of them? Thanks.May be, it is a good idea with the usb sniffer, only not for me. One sniffer crashes, another works not at all. Only the USBlyzer works. But the files that I get
every time are too small. And I don´t know why.
H.
I extracted the strings from this file and got this
@d-;|
@d-;|
0 1 8
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
DJI P1 SYS
.....................
Maybe try a different port?
You need to start the .DAT extraction via DJI 2 Assistant after you've started sniffing the USB port.
The P4 and P3 .DAT files are similar. They both get recorded onto an internal SD card that is very difficult to access physically. They are both encoded which allows the internal bus to be more efficient. In the case of the P3 the .DAT can be directly accessed via the USB port. All it takes is a file copy.
If we were able to access the P4 .DAT in the same way; i.e., just a file copy then it should be relatively simple to determine the format and DatCon would work for P4 .DAT files. @FredzMaxxUAV obtained a set of these P4 .DAT files when he had the P4 disassembled and was able to physically extract the SD card. I was then able to use some of the tools that I developed to reverse engineer the P3 .DAT file. The P3 and P4 .DATs use the same kind of format but are different enough that it would require some work to to determine the format.
The real problem is that, so far, we've been unable to get a copy of the internal SD card's .DAT file. Unlike the P3, there is no way to directly view and retrieve the internal .DAT files on the P4. Instead the P4 .DAT files are retrieved via the DJI Assistant app which then produces three files that can be sent to DJI. I've looked at these files and they are either encoded, compressed or encrypted. It doesn't make much sense to encode them. There isn't much to be gained by compressing the internal .DAT file since it already has a lot of entropy, i.e. it can't be compressed much further. But, I did look at the obvious compression schemes.
I think the files that the DJI Assistant produces are probably an encryption of the internal .DAT file. If so, then it's effectively impossible to retrieve the internal .DAT file from these files.
One possibility is to determine how the DJI Assistant produces the three file from the internal .DAT. If the bits coming across the USB to the DJI Assistant aren't encrypted then it should be possible to mimic the DJI Assistant and get those unencrypted bits. @Hans 75 attempted to use a USB sniffer but didn't get very far.
If we were able to access the P4 .DAT in the same way; i.e., just a file copy then it should be relatively simple to determine the format and DatCon would work for P4 .DAT files. @FredzMaxxUAV obtained a set of these P4 .DAT files when he had the P4 disassembled and was able to physically extract the SD card. I was then able to use some of the tools that I developed to reverse engineer the P3 .DAT file. The P3 and P4 .DATs use the same kind of format but are different enough that it would require some work to to determine the format.
The real problem is that, so far, we've been unable to get a copy of the internal SD card's .DAT file. Unlike the P3, there is no way to directly view and retrieve the internal .DAT files on the P4. Instead the P4 .DAT files are retrieved via the DJI Assistant app which then produces three files that can be sent to DJI. I've looked at these files and they are either encoded, compressed or encrypted. It doesn't make much sense to encode them. There isn't much to be gained by compressing the internal .DAT file since it already has a lot of entropy, i.e. it can't be compressed much further. But, I did look at the obvious compression schemes.
I think the files that the DJI Assistant produces are probably an encryption of the internal .DAT file. If so, then it's effectively impossible to retrieve the internal .DAT file from these files.
One possibility is to determine how the DJI Assistant produces the three file from the internal .DAT. If the bits coming across the USB to the DJI Assistant aren't encrypted then it should be possible to mimic the DJI Assistant and get those unencrypted bits. @Hans 75 attempted to use a USB sniffer but didn't get very far.
Similar threads
- Replies
- 28
- Views
- 4K
- Replies
- 17
- Views
- 3K
- Replies
- 4
- Views
- 2K
- Replies
- 3
- Views
- 6K
- Replies
- 5
- Views
- 2K